Security in cloud environments is no longer only about perimeter controls. Increasingly, protection needs to start at the infrastructure level, including how virtual machines are initialized and validated during boot.
Azure Trusted Launch is a feature designed to address this challenge. While many new deployments already benefit from it by default, an important question remains for many organizations: how can Trusted Launch be enabled on existing virtual machine scale sets?
This article explores that transition and highlights the architectural and operational implications involved.
Why upgrade existing scale sets
Many production environments were deployed before Trusted Launch became widely adopted. As a result, existing virtual machine scale sets may still be running without these additional security protections.
Enabling Trusted Launch helps strengthen the security baseline by protecting workloads against threats that target the boot process or attempt to compromise system integrity early in execution.
For organizations managing large fleets of virtual machines, upgrading existing scale sets becomes an important step in aligning with modern security practices.
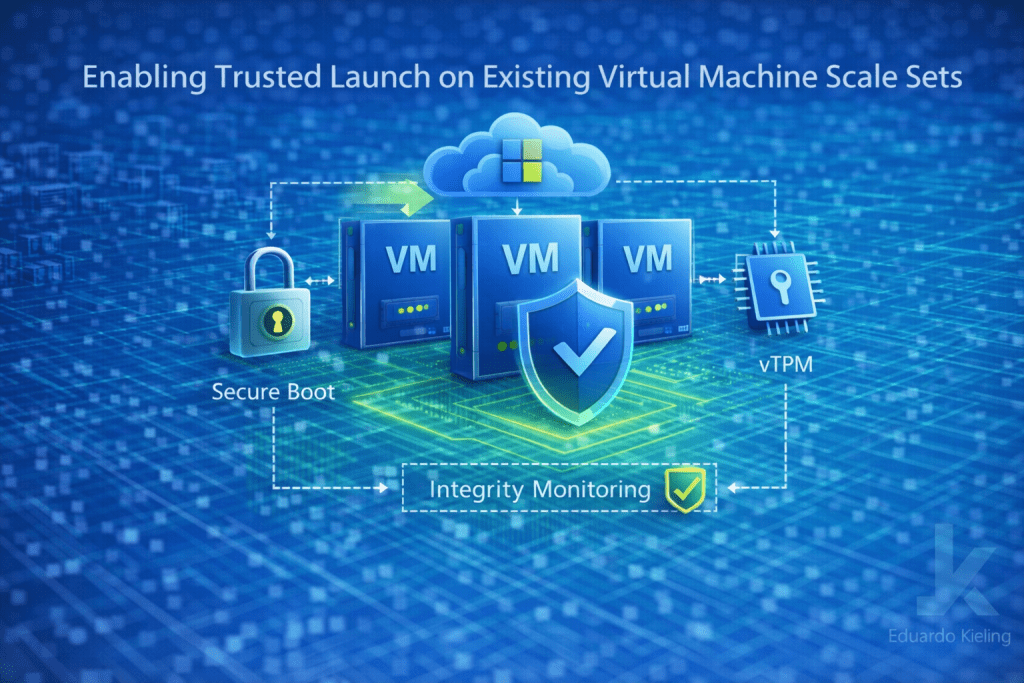
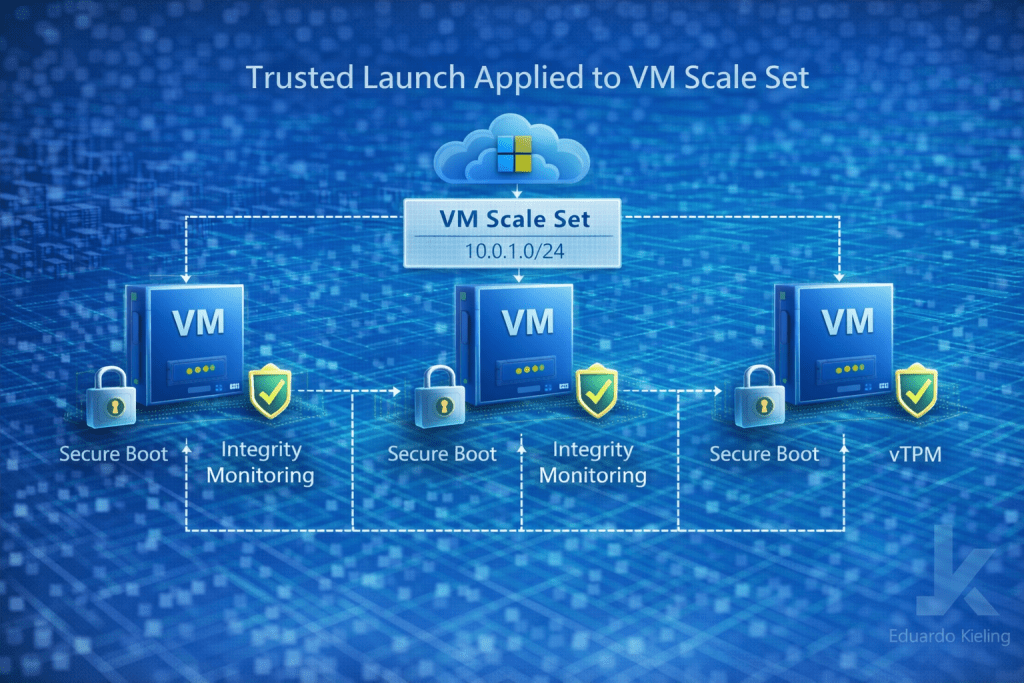
What changes with Trusted Launch
Trusted Launch introduces several protections that operate at the infrastructure level. These include Secure Boot to prevent unauthorized components during startup, virtual Trusted Platform Module (vTPM) for secure key storage and attestation, and integrity monitoring to detect unexpected changes.
When applied to scale sets, these protections extend consistently across all instances, helping ensure that each virtual machine starts from a verified and trusted state.
Implementation considerations
Enabling Trusted Launch on existing scale sets is not always a simple toggle. Depending on how the scale set was originally deployed, updates may require modifications to the underlying configuration or even redeployment of instances.
Operating system compatibility is a key factor. Only supported images and configurations can take advantage of Trusted Launch features, so validation is necessary before applying changes.
Automation pipelines should also be reviewed. Infrastructure-as-code templates may need to be updated to include Trusted Launch settings to ensure consistency across future deployments.
Impact on operations
From an operational perspective, enabling Trusted Launch may introduce changes in how scale sets are managed and updated. Rolling upgrades or instance re-creation may be required to apply the new configuration across all nodes.
This means that planning and coordination are important, especially for environments with high availability requirements.

Proper testing in non-production environments is recommended before applying changes broadly. This helps ensure that applications behave as expected with the new security features enabled.
Security improvements in practice
Once enabled, Trusted Launch enhances protection against a range of threats, particularly those targeting firmware or boot-level components. It also provides better visibility into system integrity, which can be integrated with monitoring and security tools.
For organizations focused on strengthening their cloud security posture, these improvements can play an important role in reducing risk.
Final thoughts
Enabling Trusted Launch on existing virtual machine scale sets is a valuable step toward modernizing infrastructure security. While the process may require planning and validation, the benefits in terms of protection and consistency are significant.
As cloud environments evolve, adopting secure-by-default configurations across both new and existing workloads becomes an essential part of maintaining a resilient architecture.
