Hello everyone,
Azure continues to strengthen the security posture of its compute platform, and one recent change moves in that direction: Trusted Launch is becoming the default configuration for new Generation 2 virtual machines and VM scale sets.
Instead of requiring administrators to explicitly enable this feature, new deployments will automatically include these protections by default.
What Trusted Launch provides
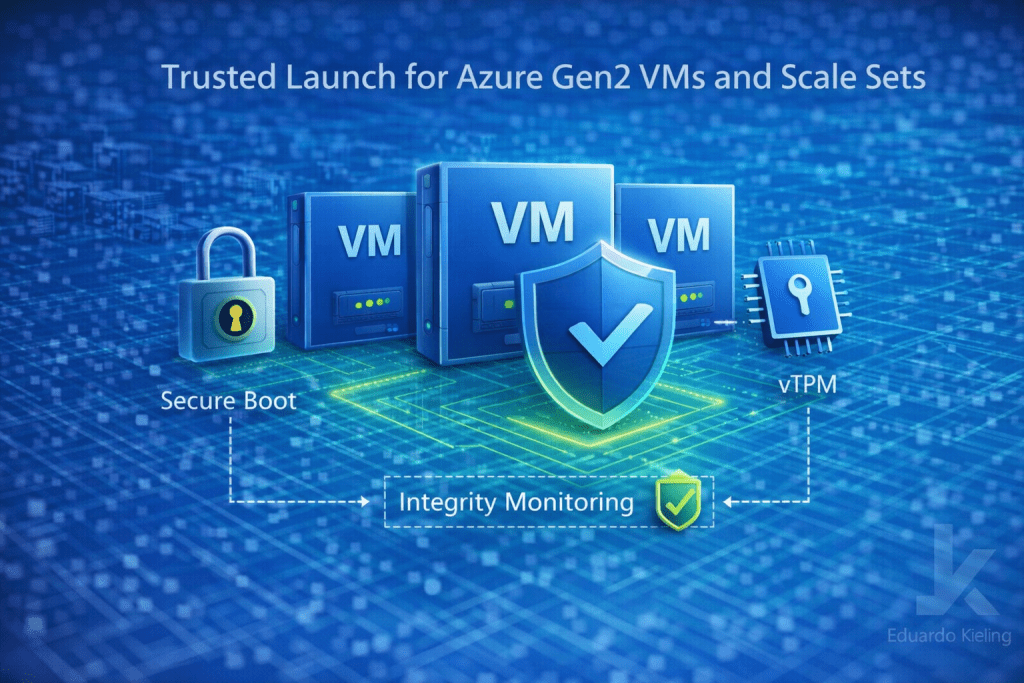
Trusted Launch is designed to protect virtual machines from advanced threats that target the boot process. It introduces several security mechanisms that help verify system integrity from the moment the VM starts.
Among the key capabilities are Secure Boot, which prevents unauthorized boot components, and virtual Trusted Platform Module (vTPM), which enables integrity verification and secure storage of cryptographic keys.
Together, these controls help ensure that the operating system starts in a trusted state.
Why making it the default matters
Security features are often available but not always consistently enabled across environments. By making Trusted Launch the default for new Gen2 deployments, Azure helps ensure that stronger security baselines are applied automatically.
This reduces the risk of environments being deployed without recommended protections and simplifies security adoption across large infrastructures.
Operational considerations
For most workloads, Trusted Launch can be enabled without requiring major architectural changes. However, it is still important to validate compatibility with operating systems, images, and deployment pipelines.
Organizations using automation or infrastructure-as-code templates may also want to review their configurations to confirm how Trusted Launch interacts with existing deployment standards.
Final thoughts
The shift toward secure-by-default infrastructure is an important trend in cloud platforms. By enabling Trusted Launch automatically for new Gen2 virtual machines and scale sets, Azure continues to reinforce security at the infrastructure level.
For cloud architects and platform teams, this means stronger baseline protection with minimal operational overhead.
