Managing network security policies in large Azure environments requires careful control over how changes are introduced. Firewall configurations directly impact traffic flow, application availability, and security posture, which means even small changes must be handled with precision.
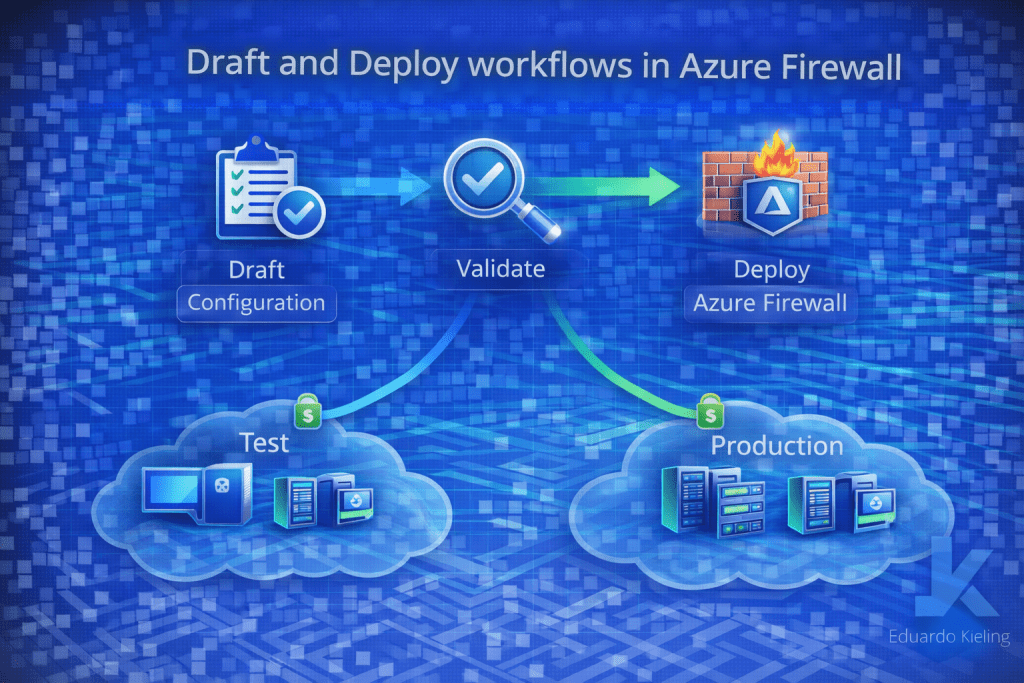
The Draft and Deploy workflow in Azure Firewall introduces a structured approach to policy management, allowing teams to prepare, validate, and safely apply configuration changes.
The challenge of firewall configuration changes
In many environments, firewall rules evolve continuously as new applications are deployed and connectivity requirements change. Without proper change management, updating firewall policies can introduce unintended disruptions or security gaps.
Traditional approaches often involve directly modifying active configurations, which increases the risk of impacting production traffic.
The Draft and Deploy workflow addresses this challenge by separating configuration changes from active policy enforcement.
Understanding the Draft and Deploy model
With this workflow, administrators can create and modify firewall policies in a draft state before applying them to production.
This allows teams to review changes, validate configurations, and ensure that policies align with expected behavior before deployment.

Once the configuration is validated, it can be deployed in a controlled manner, reducing the likelihood of unexpected issues.
Benefits for enterprise environments
The Draft and Deploy approach aligns well with enterprise change management practices. It enables teams to introduce structured workflows for firewall configuration updates, including review processes and staged deployments.
This is particularly important in environments where multiple teams collaborate on network security or where strict governance controls are required.
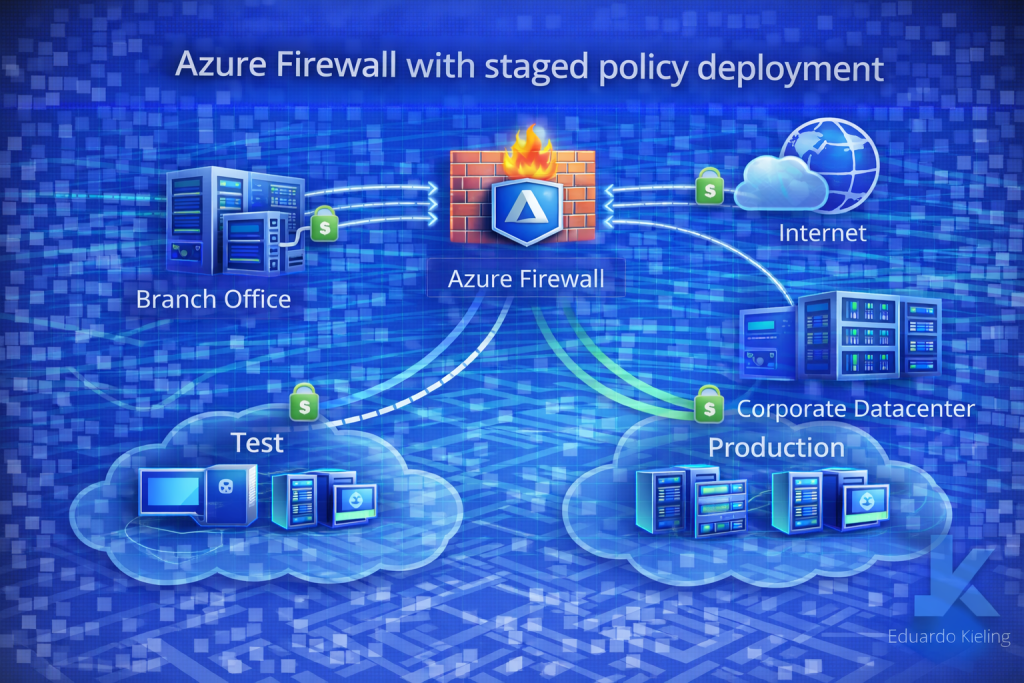
By separating drafting and deployment phases, organizations can maintain better control over policy lifecycle and reduce operational risks.
Operational considerations
Adopting this workflow requires teams to adjust how they manage firewall configurations. Processes should include validation steps, testing strategies, and coordination between teams responsible for networking and security.
Automation tools and infrastructure-as-code practices can also be integrated with the Draft and Deploy model to further standardize configuration management.
Design implications
From an architectural perspective, the ability to stage firewall policy changes supports more predictable and stable network environments. It allows architects to design systems where configuration updates follow defined processes rather than ad-hoc changes.
This contributes to improved reliability, especially in complex environments with multiple interconnected services.
Final thoughts
The Draft and Deploy workflow in Azure Firewall introduces a practical improvement to how network security policies are managed in Azure.
By enabling staged configuration changes and controlled deployment, this capability helps organizations reduce risk while maintaining flexibility in evolving their network security architecture.
