
As cloud environments grow in complexity, protecting resources is no longer limited to traditional network boundaries. Organizations are increasingly adopting architectures where services communicate internally across multiple virtual networks, subscriptions, and regions.
In these environments, the challenge is not only protecting external access but also defining clear and controlled boundaries between services. Azure Network Security Perimeter introduces a model that helps address this challenge by creating a structured security boundary around platform services.
This capability allows organizations to control how Azure services can be accessed, helping reduce exposure while maintaining flexibility in cloud architectures.
Understanding the concept of a security perimeter
Traditionally, network security relied heavily on infrastructure components such as firewalls, network security groups, and routing rules. While these mechanisms remain essential, they are often designed around virtual network boundaries.
However, many Azure services operate outside the traditional VNet model or interact with multiple environments simultaneously. In these cases, defining security controls solely at the network level may not be sufficient.
Azure Network Security Perimeter introduces a different approach. Instead of relying only on network isolation, it allows administrators to define service-level boundaries that determine how Azure resources can communicate with each other.
How the model works in practice
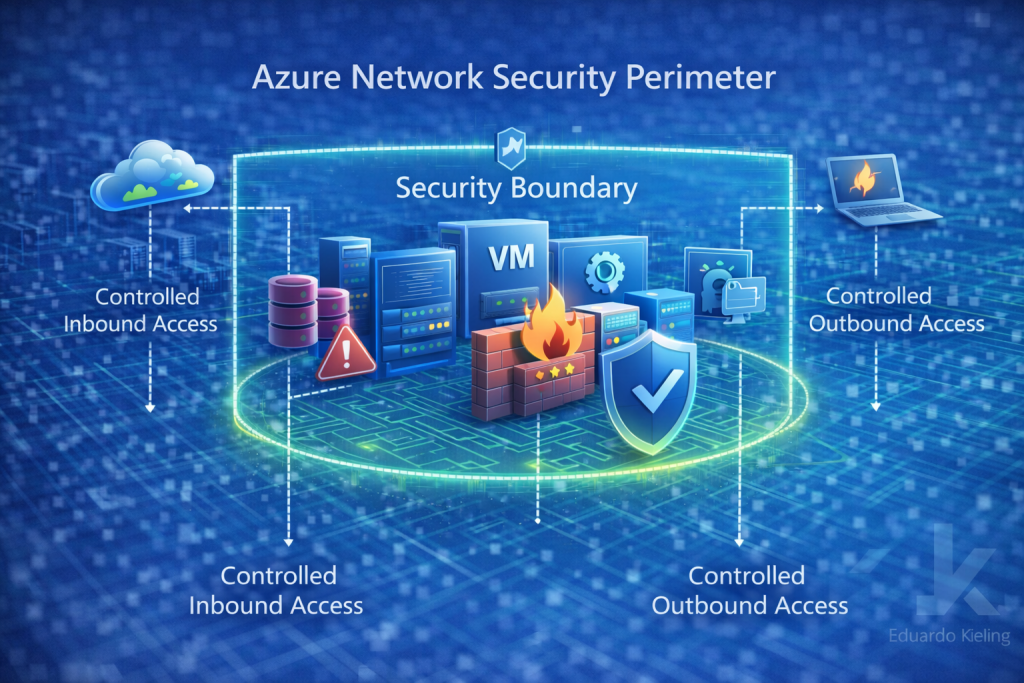
The Network Security Perimeter acts as a logical boundary around selected Azure resources. Administrators can define policies that control which external endpoints or services are allowed to interact with resources inside the perimeter.
This approach provides more granular control over service exposure. Instead of allowing unrestricted access from the internet or broad internal networks, organizations can explicitly define trusted sources and communication paths.
For example, certain data services may only accept connections from specific applications or trusted environments. With the security perimeter model, these relationships can be defined and enforced more clearly.
Implications for enterprise architectures
In large environments, cloud architectures often include multiple workloads, development environments, and shared platform services. Ensuring consistent security controls across these components can become difficult if each service is configured independently.
Azure Network Security Perimeter helps centralize this control by defining boundaries that apply across multiple services. This can simplify governance and reduce the risk of accidental exposure.
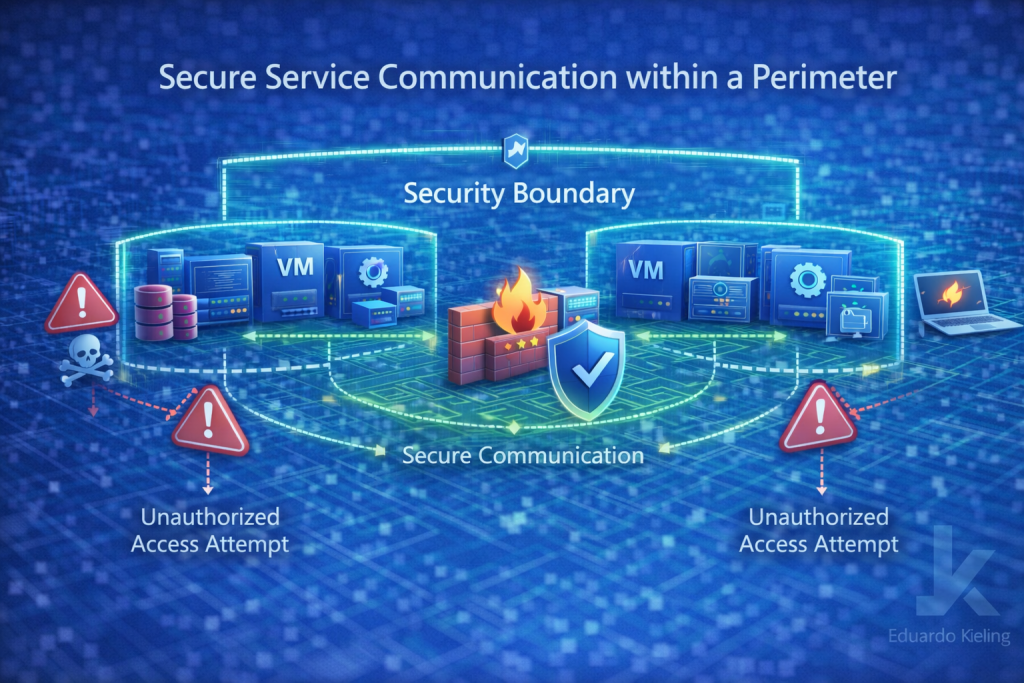
When combined with other Azure security capabilities such as private endpoints, identity controls, and network segmentation, the perimeter model adds another layer of protection that strengthens the overall security posture.
Operational considerations
From an operational perspective, adopting security perimeters requires thoughtful planning. Teams need to identify which services should be grouped within the same perimeter and define the allowed communication paths between them.
This process encourages a more structured approach to service architecture and helps ensure that access patterns are intentional rather than accidental.
Final thoughts
Azure Network Security Perimeter introduces an additional security construct that complements existing network and identity-based controls.
By enabling organizations to define secure service boundaries within Azure environments, it helps reduce exposure and improve governance across complex cloud architectures.
For teams operating large-scale Azure environments, this capability provides a valuable mechanism to better manage service access and enforce clearer security boundaries.
