Private connectivity has become a central element of secure cloud architectures. As organizations increasingly adopt platform services in Azure, controlling how those services are accessed from internal workloads becomes an important architectural concern.
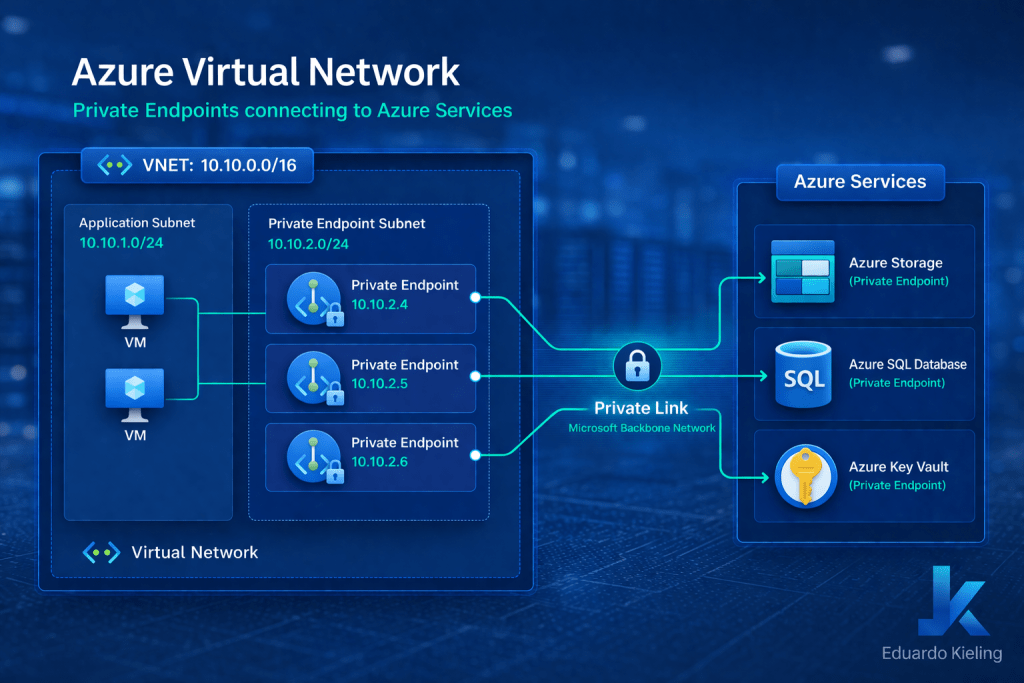
Azure Private Endpoints provide a mechanism to expose platform services through private IP addresses within a virtual network. Instead of accessing services through public endpoints, workloads communicate with them privately through the Azure backbone network.
While this capability is straightforward for small environments, designing architectures that support large-scale Private Endpoint deployments introduces additional considerations.
Understanding Private Endpoint growth challenges
In enterprise environments, it is common to deploy dozens or even hundreds of Private Endpoints across multiple services such as Azure Storage, SQL Database, Key Vault, and other PaaS offerings.
Each Private Endpoint consumes an IP address within the target subnet and introduces dependencies related to DNS resolution, routing behavior, and network governance.
Without proper planning, large-scale Private Endpoint deployments can lead to challenges such as subnet IP exhaustion, complex DNS configurations, and limited visibility across environments.
Subnet design strategies
One of the first design considerations involves subnet planning. Since Private Endpoints allocate IP addresses from the subnet where they are deployed, environments that expect significant growth should allocate sufficiently large address ranges.
In many enterprise designs, organizations dedicate specific subnets exclusively for Private EndPoints. This approach simplifies governance and avoids mixing Private Endpoint resources with application workloads.
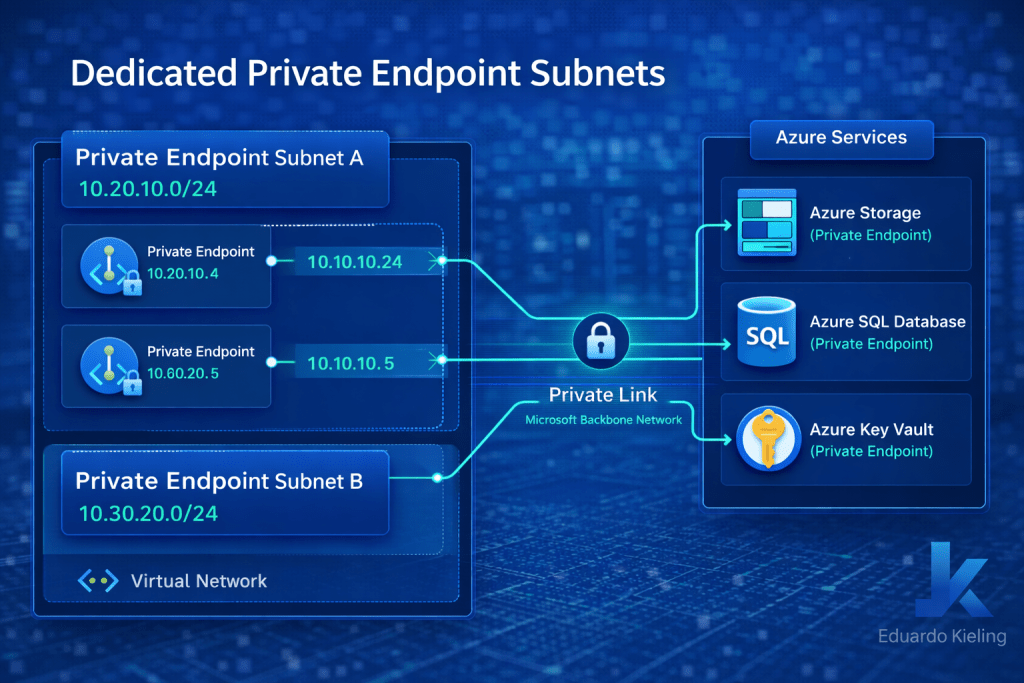
Separating Private Endpoints into dedicated subnets also simplifies operational tasks such as monitoring, policy enforcement, and network troubleshooting.
DNS architecture considerations
DNS resolution plays a critical role in Private Endpoint connectivity. When services are exposed through Private Endpoints, the DNS records must resolve to the private IP address assigned within the virtual network.
Organizations typically rely on Azure Private DNS zones to handle this mapping automatically. However, at scale, DNS architecture must be carefully designed to support multiple virtual networks and hybrid connectivity scenarios.
Many enterprise architectures adopt a centralized DNS model where Private DNS zones are hosted in a shared connectivity subscription and linked to multiple VNets.
Hub-and-spoke integration
Private Endpoints integrate naturally with hub-and-spoke network architectures. In these environments, spokes host application workloads while shared services such as DNS and connectivity reside in the hub network.
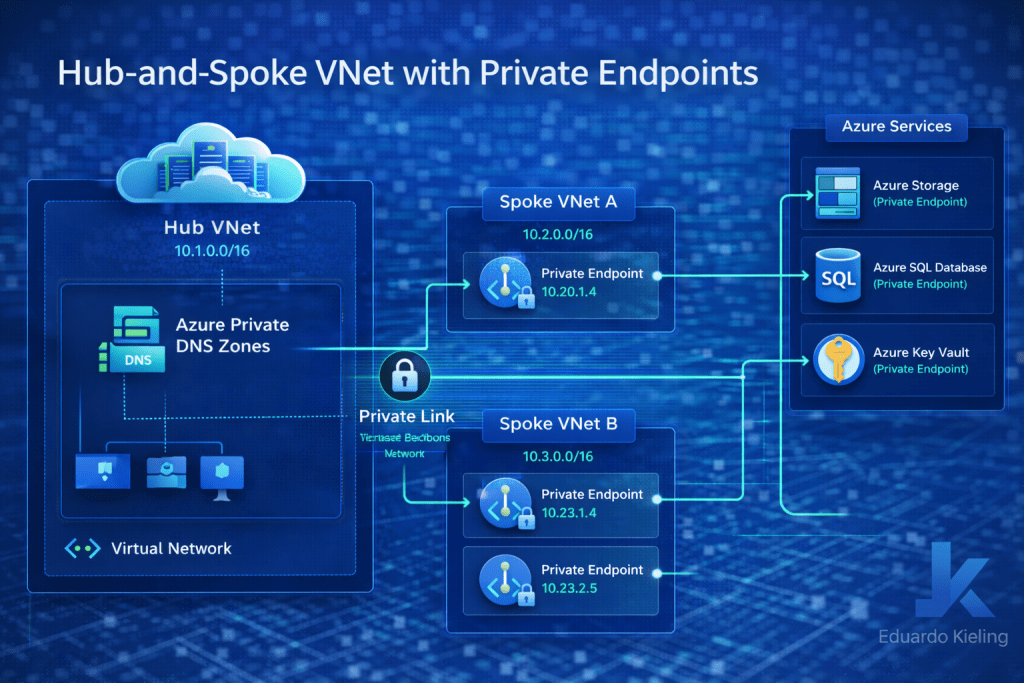
This design allows organizations to scale Private Endpoint deployments while maintaining consistent governance and operational visibility.
Governance and operational visibility
At scale, governance becomes as important as connectivity. Azure Policy can help enforce consistent configuration standards for Private Endpoints, ensuring that deployments follow predefined network design rules.
Operational monitoring tools can also provide visibility into endpoint usage, helping administrators understand how private connectivity is being utilized across the environment.
Final thoughts
Private Endpoints represent a powerful mechanism for securing access to Azure platform services. However, as environments grow, their deployment requires thoughtful planning across networking, DNS, and governance layers.
By applying scalable design patterns and maintaining clear architectural guidelines, organizations can successfully adopt Private Endpoints across large enterprise environments while maintaining network simplicity and operational control.
