Modern cloud environments require strong visibility into network activity. As organizations move critical workloads to Azure, traditional monitoring techniques based on physical infrastructure often become harder to implement. Security teams, network engineers, and operations teams still need ways to inspect traffic patterns, analyze anomalies, and troubleshoot complex connectivity scenarios.
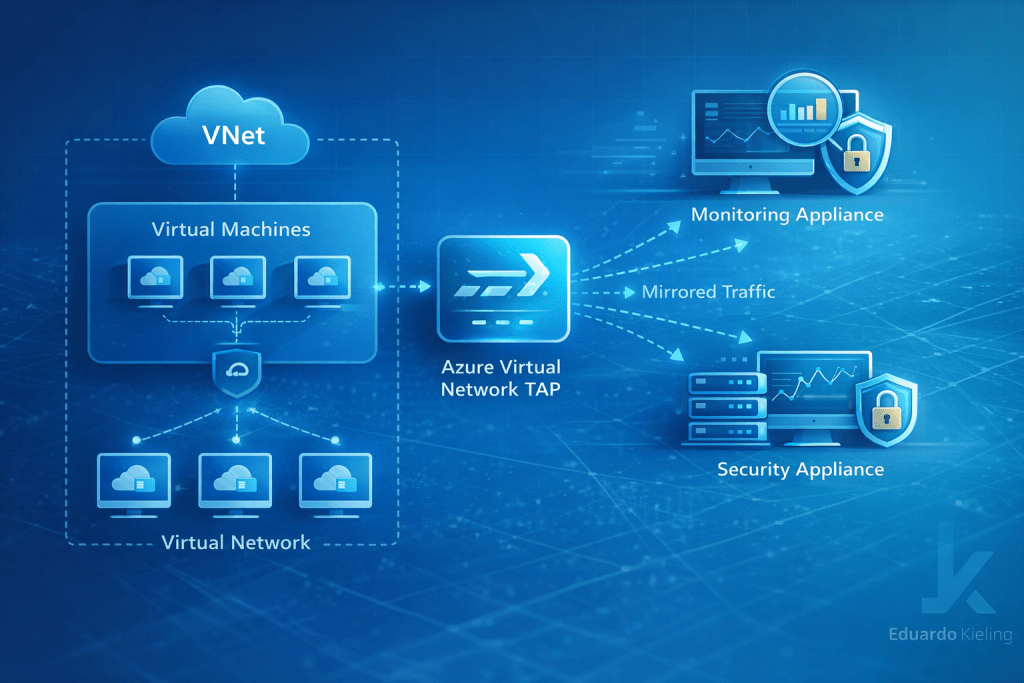
Azure Virtual Network TAP introduces a capability designed to support these needs by allowing traffic mirroring from virtual machines inside a virtual network. Instead of inserting inspection tools directly into the production path, the feature allows traffic to be copied and sent to monitoring systems. This approach enables detailed analysis without interfering with application performance or introducing additional points of failure.
Understanding the purpose of traffic mirroring
Traffic mirroring is not a new concept in networking. In traditional data centers, network devices often support port mirroring or SPAN configurations to send copies of packets to monitoring appliances. These mechanisms allow organizations to run intrusion detection systems, packet inspection tools, or advanced analytics platforms without modifying the main traffic path.
In cloud environments the challenge is different. Infrastructure is virtualized and distributed across software-defined networks. Azure Virtual Network TAP provides a native mechanism to replicate similar capabilities in the cloud, allowing architects to mirror traffic from selected virtual machine interfaces to analysis tools.
This capability is particularly useful in environments where security monitoring, forensic analysis, or deep packet inspection is required.
Where TAP fits in a cloud architecture
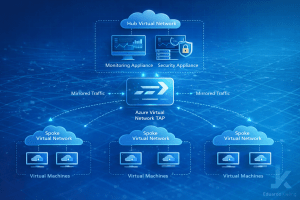
When designing enterprise architectures in Azure, monitoring components are usually placed in centralized environments that allow visibility across multiple workloads. Azure Landing Zone architectures commonly use a hub-and-spoke model where shared services such as firewalls, monitoring systems, and security tooling are deployed in a central hub virtual network.
In this model, workloads running in spoke virtual networks can mirror their traffic toward monitoring systems located in the hub. This allows security or operations teams to analyze network behavior across many environments from a single location.
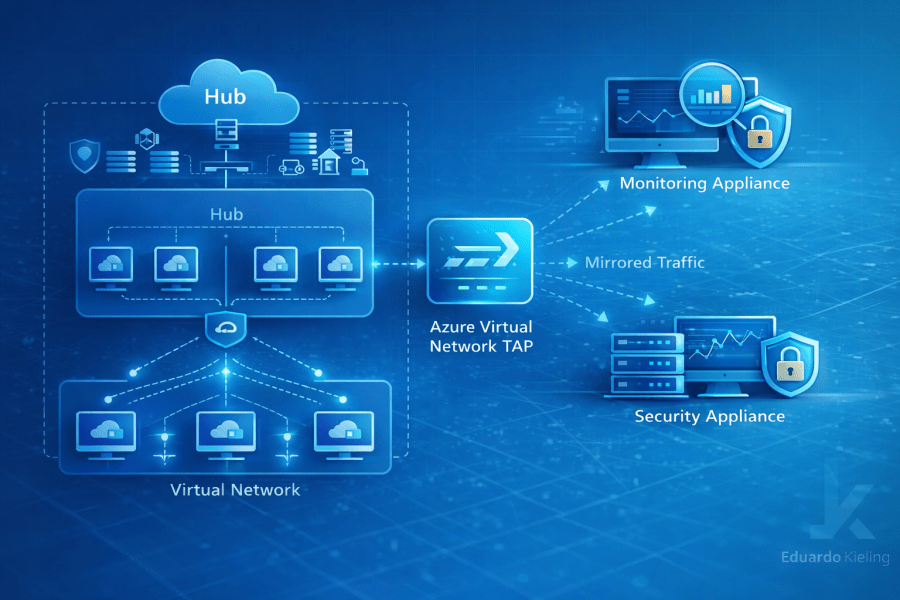
Centralizing monitoring systems helps organizations simplify operations and maintain consistent visibility across application environments. It also aligns well with security architectures where inspection tools are deployed in dedicated monitoring zones.
Design considerations for monitoring environments
Architects planning to use traffic mirroring should carefully design the environment receiving mirrored packets. Monitoring systems must be capable of processing potentially large volumes of traffic depending on the number of mirrored workloads.
Virtual machines running monitoring tools may require higher network throughput and additional compute resources. Packet capture systems, intrusion detection platforms, and analytics tools often require significant processing power to analyze mirrored traffic effectively.
Another important factor is network segmentation. Monitoring appliances should normally be placed in dedicated subnets separated from production workloads. This design helps isolate monitoring systems and ensures that traffic analysis does not affect application performance.
Selective monitoring strategies
Not every workload needs deep packet inspection. In most enterprise environments, organizations select specific systems where visibility is critical. This may include application gateways, internet-facing services, or environments handling sensitive data.
By enabling traffic mirroring only where it is required, organizations can avoid overwhelming monitoring platforms with unnecessary data. Selective monitoring also reduces operational complexity and allows teams to focus on analyzing the most relevant network flows.
Clear policies for when and where traffic mirroring should be used help maintain an efficient monitoring strategy.
Supporting security and investigation workflows
One of the most important use cases for traffic mirroring is security analysis. Many security platforms rely on packet-level visibility to detect suspicious behavior, analyze attack patterns, or investigate incidents.
By forwarding mirrored traffic to specialized security appliances or packet inspection tools, organizations can build detection capabilities that complement other Azure security controls.
These inspection platforms may analyze protocols, detect anomalies, and correlate network events with logs generated by other systems. When combined with centralized monitoring platforms and security analytics tools, traffic mirroring can significantly enhance visibility into network activity.
Operational troubleshooting scenarios
Traffic mirroring can also be extremely valuable during troubleshooting situations. Network engineers may need to inspect packet flows to understand unexpected application behavior or diagnose intermittent connectivity problems.
Capturing mirrored traffic allows teams to observe real communication patterns between services without modifying application configurations. This can accelerate root cause analysis and provide deeper insight into network interactions.
In complex distributed systems, where microservices and external APIs interact across multiple network boundaries, this visibility can be particularly useful.
Final thoughts
Azure Virtual Network TAP introduces a practical mechanism for improving network visibility within Azure environments. By enabling passive traffic mirroring, organizations gain the ability to inspect packet flows without interfering with production workloads.
When integrated into well-designed monitoring architectures, the feature can support security analysis, operational troubleshooting, and deeper insight into application communication patterns. As cloud environments continue to grow in complexity, capabilities that enhance network visibility will become increasingly valuable for organizations operating at scale.
