Security and regulatory compliance are key considerations when designing enterprise architectures in Azure. Many industries, including government, finance, and healthcare, must follow strict cryptographic standards to ensure that sensitive data is processed using validated security mechanisms.
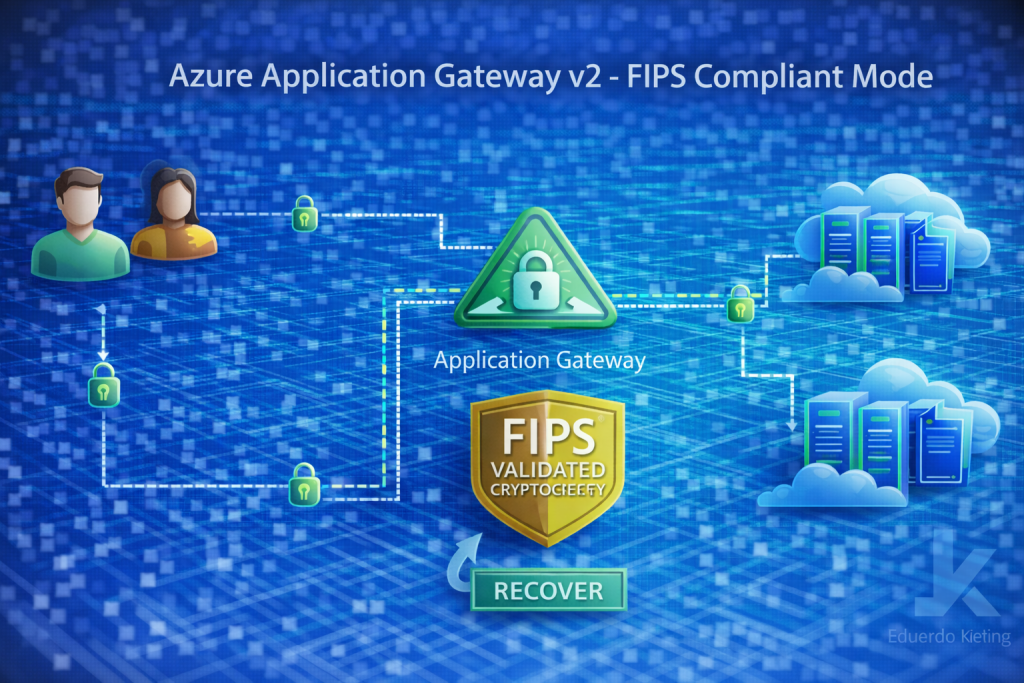
To support these requirements, Azure Application Gateway v2 introduces a FIPS compliant mode. This capability enables organizations to enforce cryptographic operations that align with the Federal Information Processing Standards (FIPS).
What FIPS compliance means
FIPS is a set of standards developed by the U.S. National Institute of Standards and Technology (NIST). These standards define approved cryptographic algorithms and security requirements used by government agencies and regulated industries.
When a service operates in FIPS-compliant mode, it ensures that cryptographic functions such as encryption, hashing, and key management follow validated implementations approved under FIPS guidelines.
For cloud architectures, this capability helps organizations meet regulatory requirements while maintaining strong security controls.
How FIPS mode works in Application Gateway
Application Gateway v2 acts as a layer 7 load balancer that handles HTTPS traffic, TLS termination, and web application firewall capabilities.
When FIPS mode is enabled, the gateway ensures that only FIPS-validated cryptographic modules are used during TLS processing.

This ensures that encryption and decryption operations adhere to recognized security standards.
Use cases in compliance-driven environments
Organizations operating under strict regulatory frameworks often require infrastructure components to meet FIPS standards. Examples include:
- Government cloud environments
- Financial services platforms
- Healthcare applications handling sensitive data
- Systems subject to strict regulatory audits
By enabling FIPS-compliant mode in Application Gateway, architects can align application delivery infrastructure with compliance requirements while still leveraging Azure-native networking services.
Architecture considerations
When designing architectures that require FIPS compliance, it is important to evaluate all components involved in the application path.
This includes load balancers, application gateways, encryption mechanisms, and backend services.
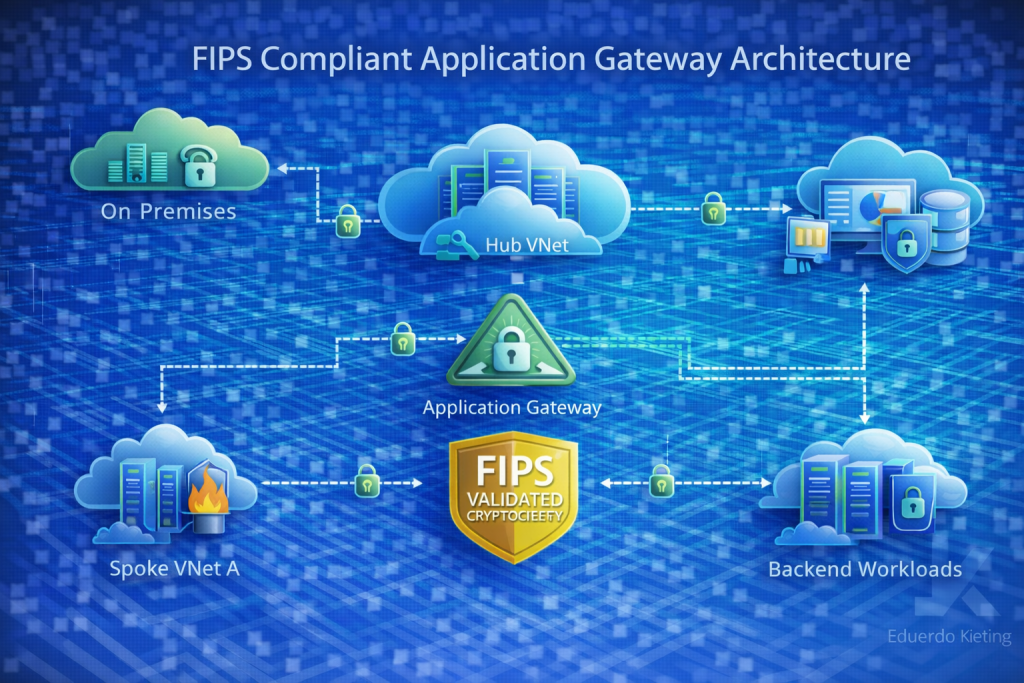
Ensuring consistent compliance across the entire architecture helps prevent gaps that could affect regulatory audits or security assessments.
Operational considerations
Enabling FIPS mode may influence the set of supported cryptographic algorithms and TLS configurations. Teams should validate application compatibility and security policies before activating the feature.
Monitoring and governance practices should also be updated to ensure that compliance settings remain consistent across environments.
Final thoughts
The introduction of FIPS-compliant mode for Azure Application Gateway v2 provides organizations with an additional capability to meet regulatory security requirements.
For environments where compliance is a critical factor, this feature allows teams to maintain strong cryptographic standards while continuing to benefit from the scalability and flexibility of Azure networking services.
