Hi everyone,
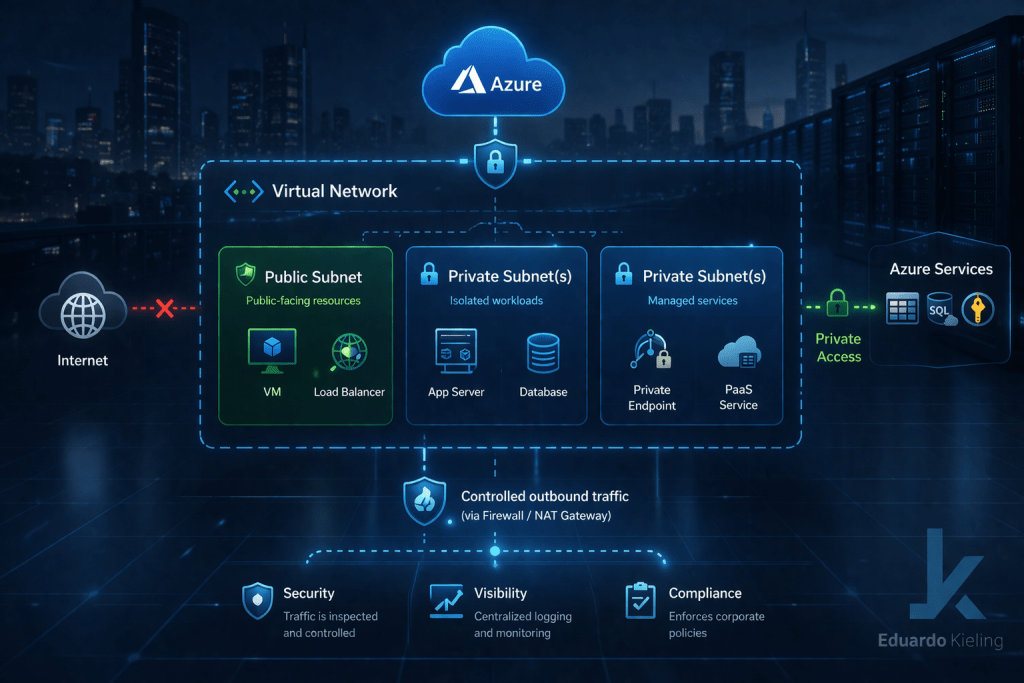
One of the topics that keeps coming up in conversations around secure Azure architectures is how to properly isolate workloads while still keeping connectivity manageable. A feature that plays an important role in this space is the concept of Private Subnets in Azure.
At first glance, it may seem like just another networking configuration, but when used correctly, private subnets can significantly improve how environments are segmented and secured.
What is a private subnet in practice
A private subnet is designed to host workloads that should not have direct exposure to the public internet. This means that resources inside the subnet operate fully within private address space and rely on controlled paths for any external communication.
Instead of allowing outbound internet access by default, these environments typically require explicit routing through controlled components such as firewalls, NAT solutions, or other inspection layers.
Why this matters for architecture
In many enterprise environments, one of the key design goals is to reduce unnecessary exposure and enforce strict traffic control. Private subnets help achieve this by ensuring that workloads cannot directly communicate with the internet unless explicitly allowed.
This creates a more predictable and secure network behavior, where all outbound traffic can be inspected, logged, and controlled.
For architects, this simplifies the enforcement of security policies and aligns well with zero trust principles.
Common design patterns
Private subnets are often used in combination with centralized networking architectures. A typical approach is to route outbound traffic through a shared hub where security services are deployed.
This allows organizations to apply consistent inspection and filtering policies across multiple workloads and environments.
Another common pattern is using private subnets for backend services, such as application tiers or databases, while frontend components are placed in controlled entry points.
Things to keep in mind
While private subnets improve security, they also require careful planning. Connectivity to external services must be explicitly designed, and dependencies such as updates, package repositories, or external APIs need to be considered.
DNS resolution, routing, and access to platform services should also be validated to avoid unexpected behavior.
Wrapping up
Private subnets are a simple but powerful building block for designing secure Azure environments. They help enforce isolation, improve traffic control, and reduce unnecessary exposure of workloads.
If you are working on landing zones or enterprise-scale environments, this is definitely a concept worth incorporating early in your network design.
