Hello everyone,
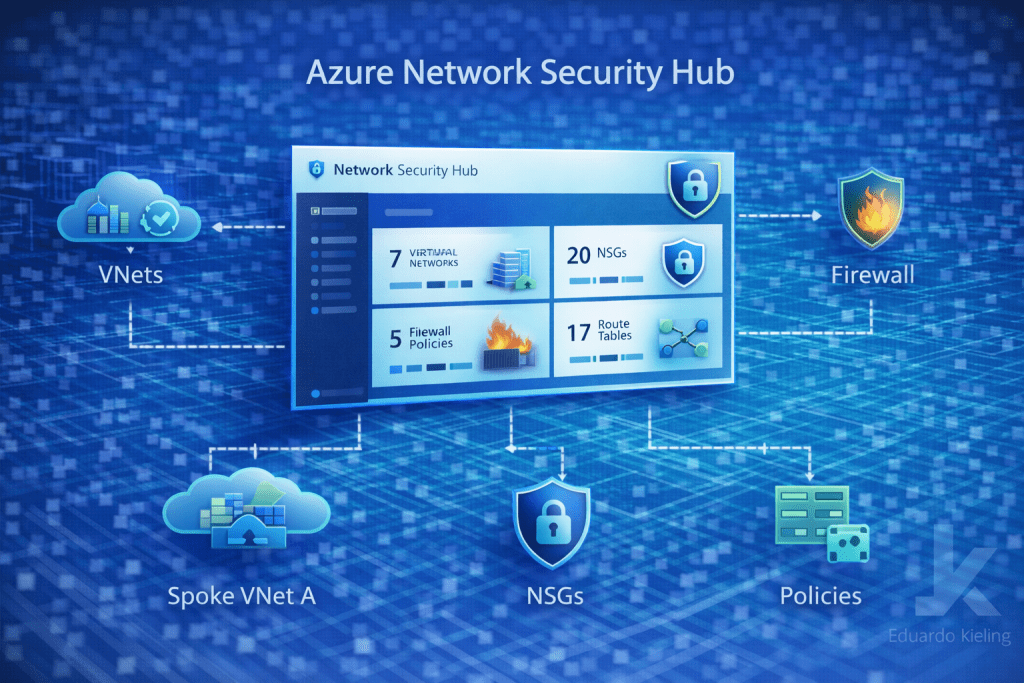
Managing network security across multiple Azure environments can quickly become complex. As organizations scale their cloud infrastructure, maintaining visibility over firewalls, network security groups, routing rules, and other controls becomes increasingly important.
To address this challenge, Microsoft introduced the Azure Network Security Hub, a centralized experience designed to simplify how security configurations are monitored and managed across Azure networking resources.
Continue reading “Overview of the new Azure Network Security Hub experience”